Trusted by thousands of businesses globally


























Netstock’s global footprint
2,200+
Global customers
20,000
Users
$25 billion
Inventory managed by Netstock
67
Countries with customers
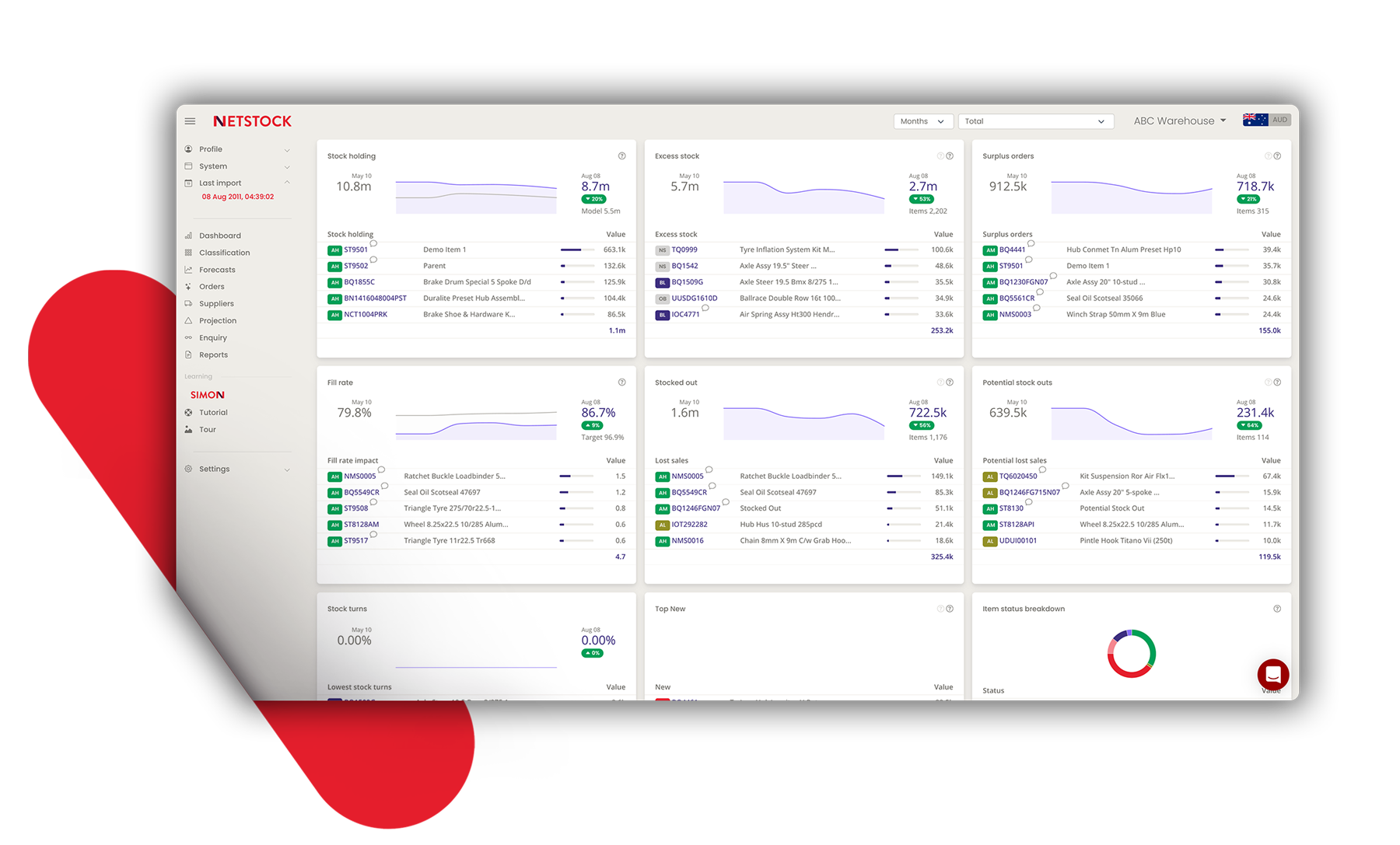
Unlock operating cash with intelligent inventory planning
Place orders quicker
Save time on planning, forecasting and ordering
Minimize stock-outs
Retain customers and increase sales
Reduce excess stock
Release cash tied up in excess inventory
Measure scenario models
Analyze supply and demand changes
The proven leader in
supply chain planning




We were able to reduce our inventory value by an impressive $1 million, thanks to Netstock
– Hartland Controls
Designed by inventory people, for inventory people
Stay agile, responsive, and profitable
See how smart inventory planning comes to life

6 Supply chain planning trends for 2023
Netstock experts share top insights to consider in 2023.
Read More

Best practices to optimize your supply chain
Enable your business to make smart decisions.
Learn More

TruAudio optimizes inventory
Inventory visibility enables TruAudio to reduce excess stock.
Watch Now
Ready to get started?
Discover how Netstock’s Predictive Planning Suite™ accelerates inventory planning.
Watch Demo











